Should you be using LUN Masking or Zoning with your storage?
When it comes to networked storage you have a few different options and should investigate them to see which option suits the needs of your business and IT infrastructure. The 3 main types of storage solutions out there are Fibre Channel, iSCSI and NAS and each has their own advantages and disadvantages. We will not be going into those specifics right now but will in a future article.
So for now we are going to be talking about zoning vs LUN (Logical Unit Number) masking and what they do and how they differ when it comes to granting access to your storage devices. It is possible to use zoning and LUN masking at the same time but it’s not a requirement. Neither one of these are used with NAS storage and zoning is only used with fiber channel storage. LUN masking can be used with iSCSI storage and fiber channel storage. Now let’s discuss LUN masking and zoning.
LUN Masking
LUN masking is the process of masking or hiding LUNs from hosts that shouldn’t see them or have access to them. If the storage doesn’t allow visibility of the LUN to a particular host then it doesn’t even exist as far as the host is concerned. By masking the LUN you prevent multiple hosts writing data to the same LUN which has the potential to cause some serious problems.
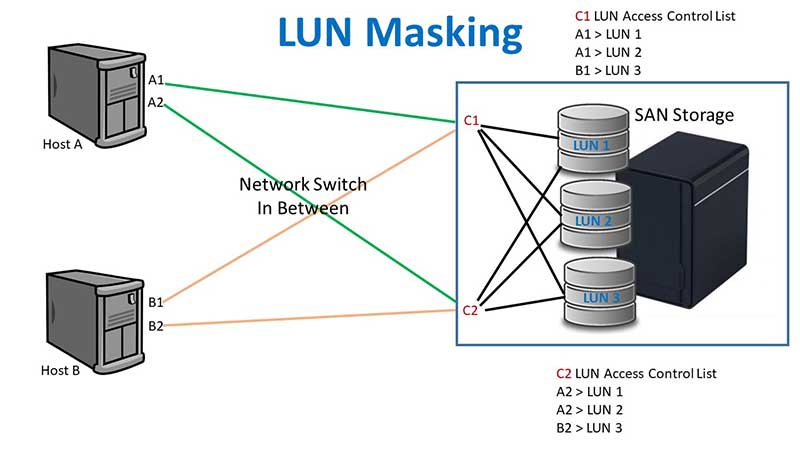
As you can see in our configuration the ACL (Access Control List) for controller 1 says that HBA A1 has access to LUN 1 and LUN 2 and HBA B1 has access to LUN 3. Then the ACL for controller 2 says that HBA A2 has access to LUN 1 and LUN 2 and that HBA B2 has access to LUN 3. To simplify, host A has access to LUNs 1 and 2 and host B has access to LUN 3. This way there is not more than one host having access to a particular LUN risking corruption on the LUN. That doesn’t mean you can’t share a LUN between hosts because that is a fairly common procedure. VMware hosts for example can have access to the same LUNs because you can create multiple datastores on a LUN to use with different hosts.
Zoning
SAN zoning is the process of separating devices, hosts and storage by creating zones where only certain devices can communicate with certain storage resources that are in the same zone. It is also used to keep hosts from communicating with each other. This zoning is done on the storage fabric and the fabric consists of the devices that connect the hosts to the storage.
Most zones are single initiator zones where you have just one initiator per zone but you can have multiple targets. At the same time initiators and targets can be members of multiple zones.
There are also 2 kinds of zoning that are commonly used, hard zoning and soft zoning.
Hard zoning – based on ports and whatever you connect to a certain port associated with a zone becomes part of that zone. This type of zoning is less secure because you can connect to a port and automatically be part of a zone.
Soft zoning – based on WWNs (World Wide Name) where you can move the devices around on the network and they will stay in the same zone because the WWN doesn’t change. If you have to replace a HBA then you will have to do some reconfiguring of the zone. There is still a threat of WWN spoofing to get around this type of security. You can also have aliases for WWPNs so you don’t have to remember the entire 64 bit hex number. This is the more popular configuration of the two.
Zones are grouped into what are called zone sets. A zone set can contain more than one zone and a zone can be in more than one zone set but there is only one zone set can be active at a time.
In the example below we have 2 hosts that each have a connection to Fabric A and Fabric B which each have a connection to Controller A and Controller B on the storage. There is a connection from the HBAs on Host 1 connected to the Prod Zone on Fabric A and the Prod Zone on Fabric B for redundancy. There is also a connection from the HBAs on Host 2 connected to the Dev Zone on Fabric A and the Dev Zone on Fabric B.
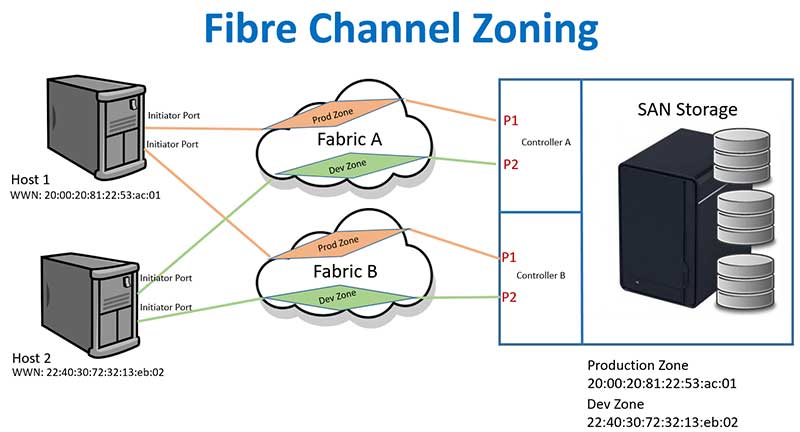
This configuration keeps Host 1 and Host 2 from communicating with each other and also keeps the Production Zone and Development Zone separate as well.
For additional training resources, check out our online IT training courses.
Check out our extensive IT book series.






