Should You Be Using a Peer to Peer Network or a Client-Server Network
Even though networking can be quite complicated, the concept itself is rather simple. What a network does is connect devices like computers, servers and printers together so they can communicate with each other. This can be done with various types of cabling such as Ethernet or fiber optic cables or even wirelessly.
In the early days of networking, things were much more simple than they are today with all of the complex switches, routers, firewalls and other devices that we use to connect our devices in the office and even across other cities, states or even countries. One of the first types of networks to be configured was called a peer to peer network. These are still in use today but are not nearly as common as client-server networks like you will see in most organizations. In this article we will discuss what each type of network is and how they differ from each other.
In the early days of networking, things were much more simple than they are today with all of the complex switches, routers, firewalls and other devices that we use to connect our devices in the office and even across other cities, states or even countries. One of the first types of networks to be configured was called a peer to peer network. These are still in use today but are not nearly as common as client server networks like you will see in most organizations. In this article we will discuss what each type of network is and how they differ from each other.
Peer to Peer Networks
Peer to Peer networks, also called workgroups were the first type of network to be used. In this type of network there is no centralized management or security and each computer is in charge of its own local users and file and folder permissions. Since there is no centralized user management, any user who wants access to resources on another computer will need to have an account on that specific computer. So if a user wants access to files on 10 different computers then that user will need 10 separate user accounts.
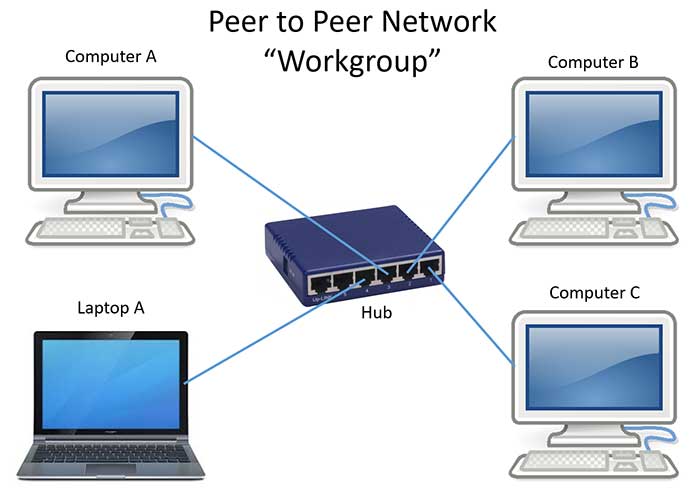
So if Sally is a user on Computer A and she wants to access files on Laptop A and Computer C then an admin on Laptop A and Computer C will need to make a user account for her and then assign the permissions she needs to be able to access those resources. You can imagine how complicated this would get as the number of computers on the network grows.
When the number of computers in a peer to peer network starts to go past 10 then you can run into problems such as slowdowns from network broadcasts and other traffic because all the traffic goes to each computer even though only the computer that it was meant to go to will accept the information. Plus many workgroup configured operating systems can only accept 10 concurrent connections at a time. So if you have a computer acting as a file server and 20 users then only 10 of them can connect to that file server at a time.
Peer to peer networks work fine for home networks or small office networks where there are not a lot of users and computers to manage. But once you get to a certain limit, that is where you need to implement something more such as a client-server network.
Client-Server Network
Just as the name says, a client-server network has clients (workstations) as well as a server (or many servers). In the diagram below the clients are labeled Computer A, Computer B, Laptop A and so on. There is also a file server and a directory server which is used to manage user accounts and access controls.
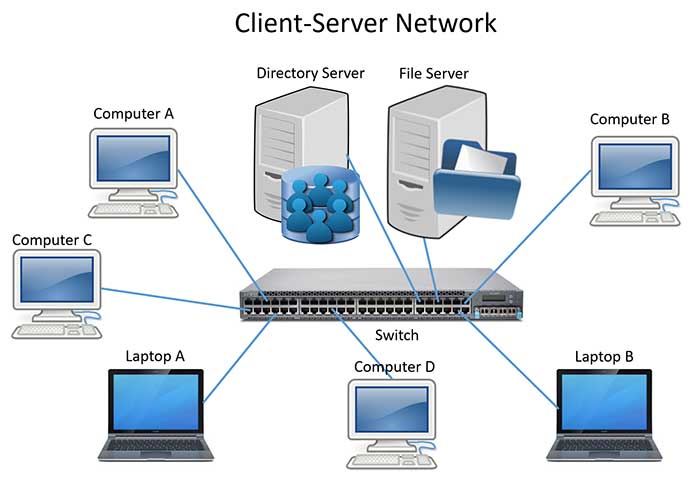
All the computers and servers connect to each other via a network switch rather than a hub like we saw in the peer to peer network even though you can use a switch for a peer to peer network as well. The main advantage here is that every user account is created on the directory server and then each computer, laptop and other servers are joined to a domain where authentication is centralized for logins and resource permissions. A domain is a centralized way to manage computers, users and resources and each computer joins the domain and each user is created as a domain user. So if a user named Joe on computer C wants to access files on Laptop B they can do so assuming their user account is allowed to. There is no need to make a user account for Joe on Laptop B or any other computer on the network besides the initial user created on the directory server.
By using a switch rather than a hub reduces broadcast traffic because the switch knows what port each computer is connected to and doesn’t have to go to each computer or server to find the one it is trying to get to. Switches can be thought of as “smart” hubs or hubs can be thought of as “dumb” switches.
The client-server model is also very scalable and the amount of concurrent connections to a server is only limited to the licensing model in place and eventually the hardware limits in regards to network bandwidth and server capacity. Directory servers can handle managing thousands of users with little hardware resources needed.
The downsides of the client-server model include:
- Increased costs because servers are more expensive that computers and network switches are more expensive than hubs.
- More difficult to implement and maintain because of its complexity.
- Single point of failure if a directory server goes down and none of your users can log in. This is often bypassed by having multiple directory servers (or domain controllers).
Overall if your environment has many resources and you want to centralize management of your users and computers then you should go with the client-server model. If you only have a few computers and users then a peer to peer configuration should work just fine. Plus you can reconfigure it to a client-server model in the future if needed.
For additional training resources, check out our online IT training courses.
Check out our extensive IT book series.