Last Updated on April 28, 2026
Create a private secured folder that only you can access
Sharing a single computer with family members or coworkers is common, but it usually comes with a major privacy concern: you do not want everyone else reading your personal files.
By default, Windows computers use the exact same file system and folder structure for every user who logs onto that machine. If you keep your personal files in public folders like the C: Drive root, anyone can open them.
If you save your files in your dedicated “Users” folder (like Documents or Pictures), you are generally protected from standard users. However, if another user on that computer has Local Administrator rights, they can completely bypass those basic protections and snoop through your profile.
If you want to create a hyper-secure folder that completely locks out everyone, including the other Administrators you have to modify the advanced NTFS security permissions.
1. How Default Windows Permissions Work
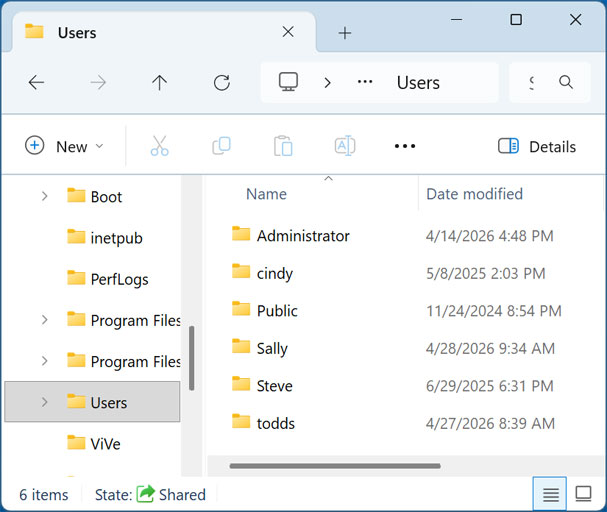
When multiple users log into a Windows 10 or Windows 11 computer for the first time, the operating system creates dedicated profile folders for them based on their username. In our example below, you can see that “Administrator,” “Steve,” and “Cindy” all have profile folders sitting inside the main Users directory.
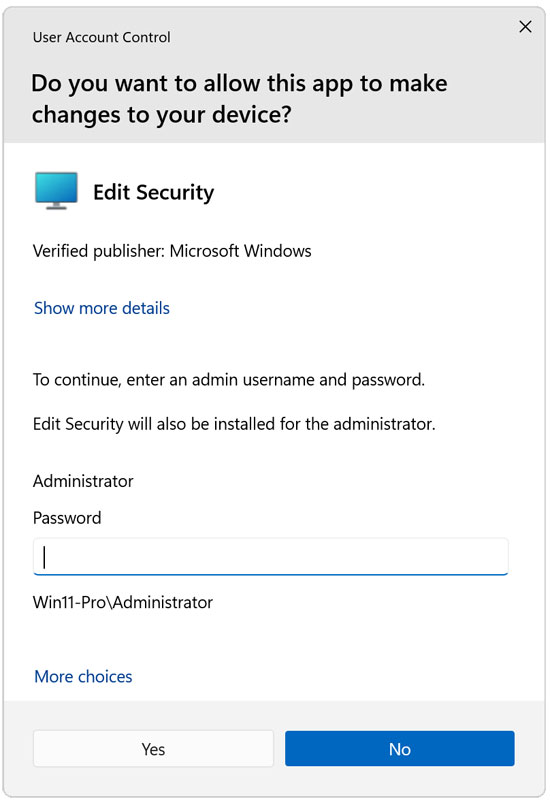
If a standard user (someone without admin privileges) tries to open another user’s personal folder, Windows will immediately block them with a permission error message. It will then throw a User Account Control (UAC) prompt asking them to type in an administrator password. If they don’t know it, they cannot get into those files.
2. Creating a Custom Locked Folder
So, what do you do if you want to lock down your files from someone who actually does have administrative credentials? You have to strip away their default inheritance rights.
In our scenario, we have two users: Cindy and Steve. Cindy wants to create a highly secure folder on the root of the C: Drive called “Cindy’s Stuff.” She wants to ensure that Steve (who is a local admin) absolutely cannot open it.
- Create the new folder on your computer.
- Right-click the folder and choose Properties.
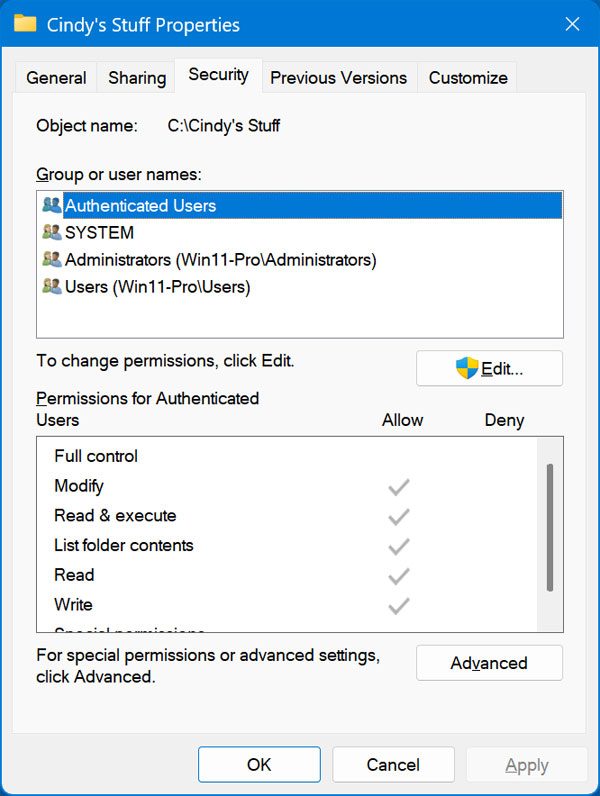
- Click on the Security tab at the top.
Here you can see the access permissions. The “Authenticated Users” group contains anyone who has logged in with a password. The “SYSTEM” account is used by Windows background services. The “Administrators” group contains anyone with admin rights (like Steve), and the “Users” group contains standard accounts.
3. Granting Yourself Exclusive Control
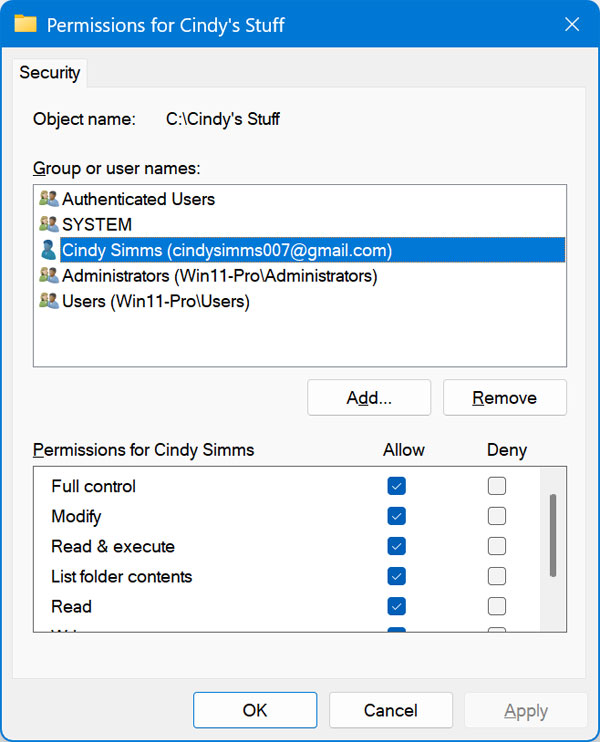
Right now, everyone has access. We need to explicitly tell Windows that Cindy is the ultimate owner of this folder.
- Click on the Edit button.
- Click the Add button.
- Type your exact username (in this case, Cindy) into the object name box and click OK.
- Click on your newly added username to highlight it.
- In the permissions box below, check the box for Full control under the Allow column.
- Click OK.
4. Breaking the Folder Inheritance
Now we want to remove everyone else’s permissions so only Cindy remains.
- Go back to the folder’s Properties window and click the Security tab.
- Click Edit.
- Click on Authenticated Users to highlight it, and then click Remove.
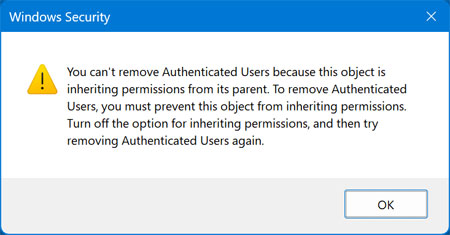
You will immediately get a warning message stating you cannot remove them because the object is “inheriting permissions from its parent.” Because this folder sits inside the C: Drive, it automatically copies all the security rules of the C: Drive. We have to sever that connection.
To fix this, close the error boxes and go back to the main Security tab for the folder.
- Click the Advanced button near the bottom.
- On the new Advanced Security Settings window, look near the bottom left corner and click the button that says Disable inheritance.
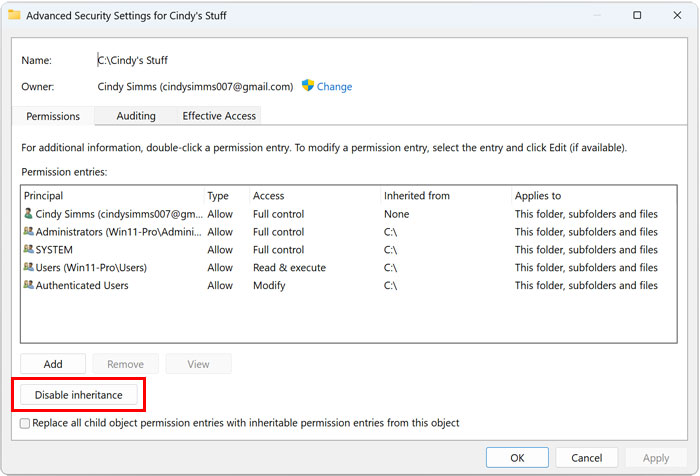
Windows will immediately prompt you with a critical choice regarding what to do with the existing rules.
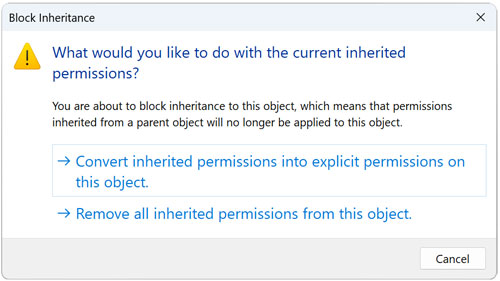
You can either “Convert” the inherited permissions into explicit permissions (which safely keeps the current rules but allows you to delete them one by one), or you can “Remove all inherited permissions” to wipe the slate completely clean.
5. Removing the Unwanted Users
If you choose “Remove all,” it will automatically delete everyone, including the critical SYSTEM user, which Microsoft does not recommend.
The safer IT method is to choose Convert inherited permissions into explicit permissions.
- Click the Convert option.
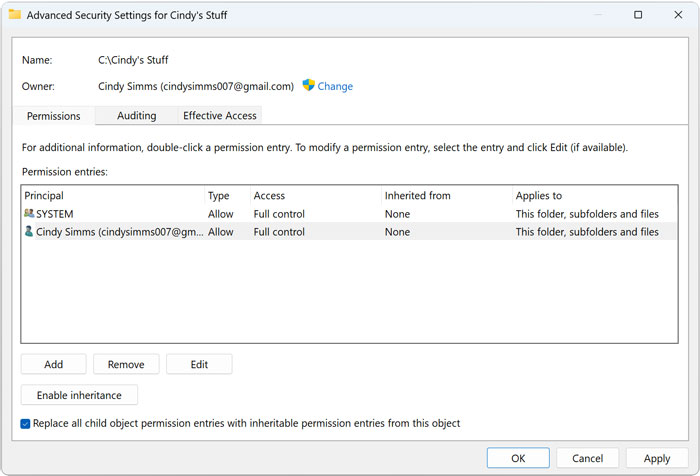
- You will be returned to the Advanced window. Now, you can manually click on the “Administrators” group, the “Users” group, and the “Authenticated Users” group and click the Remove button for each one.
- Leave ONLY your specific user account (Cindy) and the SYSTEM account in the list.
- Finally, check the box at the very bottom that says Replace all child object permission entries with inheritable permission entries from this object. This ensures that any new files you drag into this folder will automatically be locked down by these new rules.
- Click OK and click Yes to confirm the security warning.
6. Verifying the Security Configuration
Now, Cindy can confidently add her personal files to the new folder. Because we stripped away the Administrator group permissions, Steve is no longer allowed inside.
When Steve (the local admin) double-clicks the folder, he will be greeted with a “You don’t currently have permission to access this folder” message.
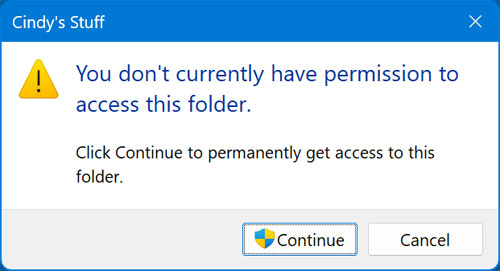
Even if Steve clicks the “Continue” button with his administrator badge icon, he will be hit with a hard “Access Denied” message, completely preventing him from opening the folder, viewing the file names, or copying the data.
Pro Technician Troubleshooting and FAQ
Can an Administrator bypass this folder security?
Yes. While this NTFS permission trick successfully stops casual snooping and blocks standard access, a knowledgeable IT technician who holds Local Administrator rights can bypass it. Because an Administrator has ultimate authority over the operating system, they can go into the Advanced Security settings and forcefully “Take Ownership” of the folder, allowing them to rewrite your rules and put themselves back on the access list.
How do I truly encrypt a folder so no one can read it?
If you want absolute, military-grade security that even a skilled Administrator cannot bypass, you must use encryption. Windows 10 and 11 Pro and Enterprise editions include a built-in feature called EFS (Encrypting File System). Right-click your folder, go to Properties, click the Advanced button under the General tab, and check the box for “Encrypt contents to secure data.” This ties the folder cryptographically to your specific Windows login password. Even if an Administrator takes ownership of the folder, the files inside will be complete gibberish without your password.
What happens if I forget to leave the SYSTEM account on the permissions list?
If you aggressively delete every user from the folder except yourself, you might accidentally break your antivirus software or your automated backup routines. Background apps like Windows Defender run under the SYSTEM account. If SYSTEM is not allowed to read the folder, your files will not be scanned for viruses and may not be backed up to your external hard drive. Always leave SYSTEM on the access list!
For additional training resources, check out our online IT training courses.
Check out our extensive IT book series.