Last Updated on March 22, 2026
Secure your public resources in a DMZ (Demilitarized Zone)
With today’s constant threats from all over the world comes the need to make sure that your valuable assets are protected from cyber criminals and others that want to do you harm or steal your information. It’s hard enough for many people to keep their home computers secure so imagine how hard it is for big companies with hundreds of servers, workstations, printers and other equipment.
Now firewalls are nothing new and we have been using them for years in the form of hardware devices or software installed on a server and they do a pretty good job of keeping our internal resources secure. But what if you have resources that you want to share with the public such as a web server or FTP server yet you still don’t want to have it wide open for everyone to access as they please.
This is where a DMZ or Demilitarized Zone (sometimes called a perimeter network) comes into play and what it boils down to is a special area on your network that is accessible from the outside world and also from inside your organization. Inside this DMZ you can place your devices or resources that you want users outside of your organization like on the internet to be able to access. Like mentioned above you would put things such as a web server in a DMZ so that its accessible on the Internet but you also have access to it via your internal network in order to make change to the server and so on. You might also use a DMZ server for a remote access server which allows home users access internal resources over the internet.
As you can see from the diagram below we have the Internet on the left that is connected to the perimeter firewall on the left. Or we should say the firewall is connected to the Internet. Then that perimeter firewall has a connection to our resources within the DMZ such as the web and FTP servers. Then the internal firewall connects to those DMZ resources and connects them to our internal network on the right. Keep in mind that this is just a general configuration and these DMZs can be much more complicated and also be created logically rather than with physical hardware. You can also configure one with only 1 firewall with multiple interfaces that connect to the different areas of the network.
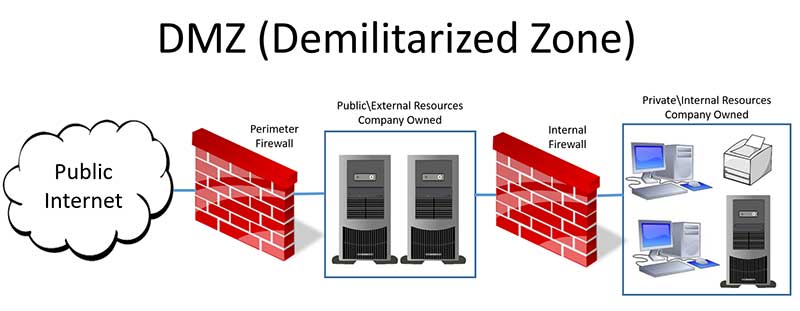
Now the connection between the firewalls and the resources is not the same on both sides. For example the connection through the firewall from the internal network to the DMZ servers may be wide open allowing all kinds of services to pass through the firewall since you wont be as concerned with security going from internal to DMZ in most cases. But connections from the DMZ server to the internal network will be locked down with only the minimal amount of access needed for communication or maybe even blocked completely. Firewalls have incoming and outgoing rules which determine what kind of traffic can pass in what direction.
For the traffic coming to the DMZ from the Internet it will be restricted to only the services and ports that are needed to communicate with those DMZ servers. For example the HTTP and HTTPS service would be allowed to the web server as well as ports 80 and 443 to make sure secure and non secure web traffic goes though the perimeter firewall. And for the FTP server it may be locked down to only the FTP service and port 21 unless other services and ports need to be opened.
You may not have a use for a DMZ on your home network unless you are running a web server or maybe a gaming server from your house and have a static public IP address so that users on the Intenet will be able to get to your servers without you needing to worry about having your IP address change on you. For corporations that have public resources it’s a must have and needs to be setup correctly in order to prevent the wrong type of people getting to resources in your DMZ that they shouldn’t be or even worse getting into your internal network. So make sure you do your homework before trying to set one up!
For additional training resources, check out our online IT training courses.
Check out our extensive IT book series.