Watch Out For Those DNS Leaks
DNS servers form a crucial part of the web. They act as the link between the internet protocol addresses and the Domain Name System. DNS servers receive traffic from various sources. Because of this, they are not safe areas for privacy. DNS servers are often ISP companies who can use the data that they get from users in any way they like. Regulatory authorities do not have much oversight over these companies and user data can often be misused for marketing purposes. A DNS leak results in the leak of user information when a person is using a VPN. There are several kinds of DNS leaks. Let’s look at some of the common causes of such leaks and how they can be fixed.
1. Poorly configured network
Improper network configuration is the number one cause of DNS leaks. This usually happens when you are using multiple networks at different times. When the connection you are using changes, so does the DHCP settings. If you have not configured the settings to ensure that your devices do not automatically assign unsafe DNS servers, then a DNS leak can occur even though you are using a VPN. In order to fix this, you need to assign the DNS provided by your VPN as your automatic gateway. In case this is not possible, a manual configuration to choose an automatic DNS server should suffice.
2. IPv6 to IPv4 conversion
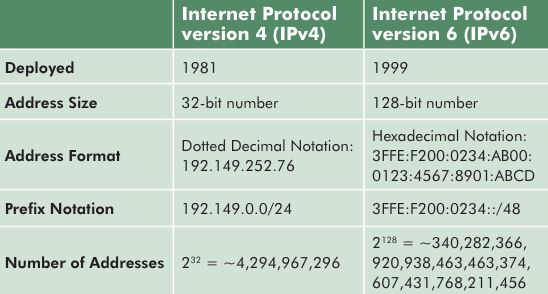
The internet has been dominated by the IPv4 address format for many years now. This type of address has a 32-bit code that identifies the IP of a particular machine. The IPv4 technology is nevertheless outdated. It is slowly losing favor to the newer IPv6 technology. Unfortunately, VPN users are not protected from DNS leaks when an IPv4 request is sent over an IPv6 tunnel. As GoBestVPN has observed, most VPN servers use the older technology and unless the VPN has the new tunnels, information will be leaked unintentionally. This problem has a simple fix – getting a VPN provider that supports IPv6. Doing this will ensure that none of your traffic is exposed to third-parties.
3. Windows features
Another source of DNS leaks is the operating system. Windows has a specific feature that allows the computer to look for the fastest DNS server when a user is connected to the internet. This feature is baked into the system and it is meant to provide the fastest speeds to users. Unfortunately, the feature automatically selects the fastest DNS servers without considering the privacy needs of the computer user. In order to bypass this feature, a specific tool that overlooks the feature is needed. Some VPN providers have such tools in the form of plugins. To disable the feature from the source though, an edit on the Local Group Policy will suffice.
4. Transparent DNS Proxies
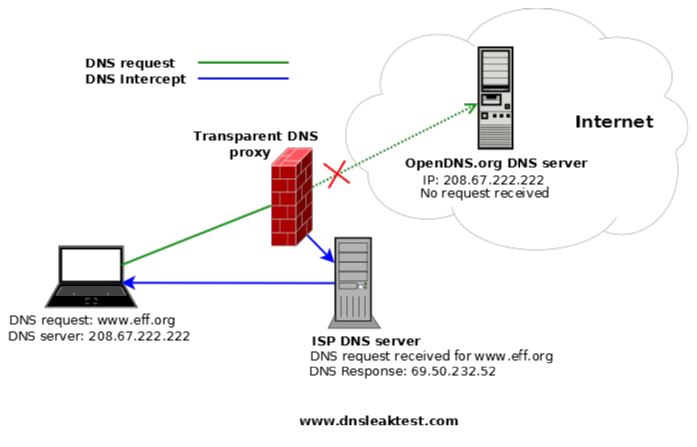
Transparent DNS Proxies are often used by ISPs to force their own servers on their network users. This is done by intercepting the web traffic coming from the network users and redirecting it over a different server that the ISP has control over. The process leaves your information exposed. In order to combat transparent DNS proxies, you need a VPN provider who allows you to block outside DNS servers. Most VPN providers can support the process through a simple edit of the configuration files. If your service provider does not support this, you can opt for a different provider who gives the option.
5. Teredo technology
Teredo is used by Microsoft to solve compatibility issues between IPv6 and IPv4. As stated earlier, the different IP versions are often a cause of DNS leaks. When used over a VPN though, Teredo might often overlook the VPN settings and expose your data. DNS leaks from Teredo can be fixed by disabling the feature. This can be done via the command prompt. Disabling Teredo is a safe measure and it does not leave your data exposed. You should, however, disable the feature when you are using a VPN.
Apart from fixing DNS leaks, you also need to take measures to ensure that the leaks do not occur in the future. You can do this by choosing an independent server and by using a firewall to ensure that all traffic goes through your VPN. Performing DNS tests regularly and installing a monitoring software can also work well.