Last Updated on March 22, 2026
In today’s fast paced mobile society everyone is connected to everything at all times with their laptops, tablets and smartphones. It’s almost like if you aren’t “connected” 24/7 you are doing something wrong. And when people can’t access the information they want or need instantly then they start to panic.
Of course people want to be connected to their work as well but most of the time you can’t take everything from work home with you so you need a way to access resources at work such as your desktop computer or file server. The way people accomplish this is by using a VPN or Virtual Private Network connection from their home or other location and connect directly to their work either into the network itself or directly to a specific computer. This way they can use their home (or remote) computer as if it was actually on the network at the office or they can do a remote connection to their actual work computer on their desk.
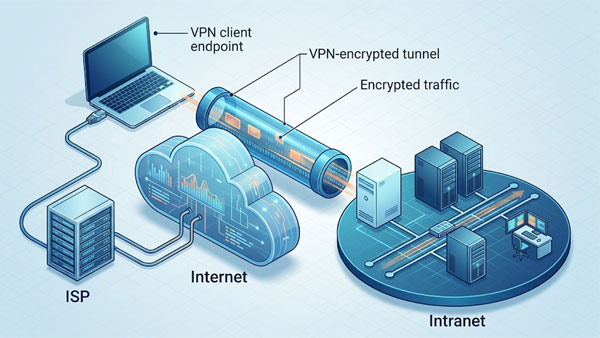
The VPN connection is accomplished by making a dedicated secure tunnel through the internet from the remote location to the destination location. The traffic is encrypted so anyone intercepting it will not be able to read it. When it comes to types of VPNs most people either use a remote access VPN where you have client software running on the remote computer and you connect into your corporate firewall with a username and password which allows you access to the network. From there you can either have unrestricted access to the network or be restricted to accessing one or more individual computers or other resources. Another type is a site to site VPN where the connection is always up and running allowing one or more user from the remote site access to the other site. This type of connection can be either one way or both ways depending on your needs.
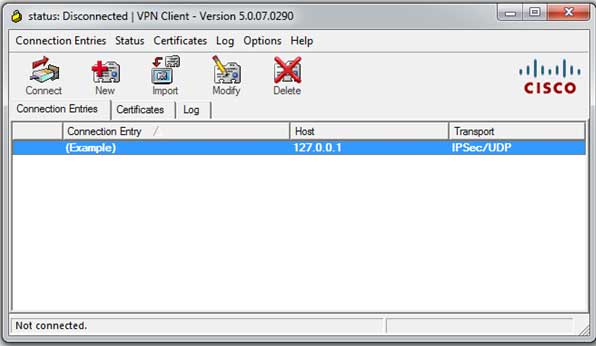
For the VPN clients you will use the one that matches the type of firewall you will be connected to at the remote site. Common brands are Cisco, Checkpoint, Palo Alto Juniper and SonicWall. You can also setup Windows and Linux servers to act as firewalls for VPN access if you don’t want to invest in an actual hardware firewall. Some network routers can also have VPN functionality built in and there are also other VPN web based services like SecureLink that will use appliances at the corporate site and the VPN connection will be initiated via a web browser.
There are many encryption methods/protocols used for VPN connections and some are more secure than others so you need to make sure the devices on both ends support whatever protocol you decide to use. Some examples are PPTP, L2TP, IPsec, OpenVPN, SSTP and IKEv2. Setting up a VPN connection is not super hard but it will take a little homework on your part to make sure you get things right and make sure you have adequate security in place.
Check out this helpful link for more information about how VPNs work and what you can do with them.
See Next:
OpenVPN vs. PPTP