Last Updated on March 28, 2026
In today’s digital landscape, where the internet serves as both a lifeline and a potential threat vector, protecting your computer from malicious attacks is paramount. One of the primary defenses your computer has built into it is the Windows Firewall. In this article, we will be discussing the workings of the Windows Firewall and how it serves as a crucial barrier against internet-based attacks.
Understanding the Windows Firewall
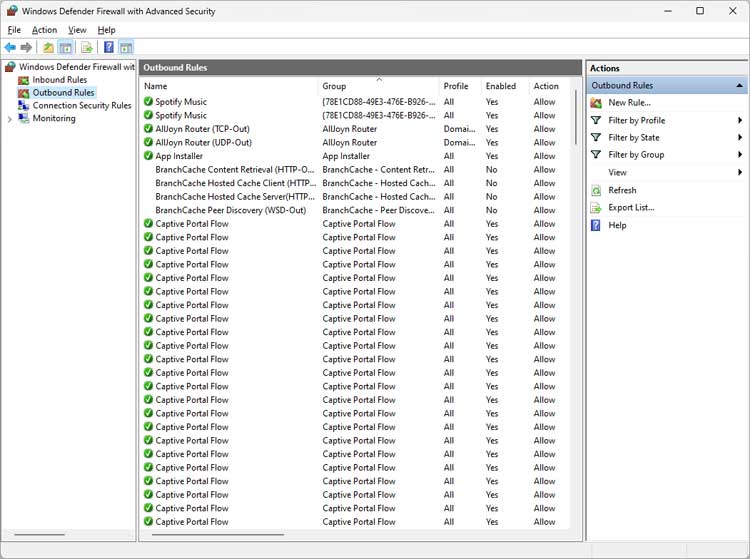
The Windows Firewall acts as a barrier between your computer and the vast expanse of the internet, regulating the flow of data to and from your system. It operates by inspecting incoming and outgoing network traffic and determining whether to allow or block specific connections based on predefined rules.
Key Features and Functionality
- Packet Filtering: At its core, the Windows Firewall employs packet filtering to scrutinize individual data packets as they traverse the network. By analyzing various attributes such as source and destination IP addresses, ports, and protocols, the firewall can make informed decisions about permitting or denying traffic.
- Stateful Inspection: Unlike basic packet filtering, which evaluates each packet in isolation, stateful inspection considers the context of network connections. It maintains a state table that tracks the state of active connections, enabling the firewall to discern legitimate traffic from potentially harmful ones based on the connection’s history and characteristics.
- Application Control: In addition to traditional port-based filtering, the Windows Firewall offers application-level control, allowing you to create rules based on specific programs or processes. This feature is particularly valuable for safeguarding against unauthorized applications attempting to access the network without your knowledge.
- Customizable Rulesets: Windows Firewall provides a range of predefined rules covering common network services and applications. However, users also have the flexibility to create custom rules tailored to their specific needs, granting granular control over network traffic based on criteria such as IP addresses, protocols, and port numbers.
Protection Against Common Threats
- Malware and Exploits: Malicious software and exploits often attempt to infiltrate systems by exploiting vulnerabilities in network protocols or services. The Windows Firewall serves as a first line of defense against such threats, blocking unauthorized attempts to exploit known weaknesses and preventing malware from communicating with command-and-control servers.
- Denial-of-Service (DoS) Attacks: DoS attacks aim to overwhelm a system or network with a flood of traffic, rendering it unresponsive or inaccessible to legitimate users. The Windows Firewall can mitigate the impact of DoS attacks by filtering out malicious traffic and limiting the rate of incoming connections, thereby preserving system resources and maintaining service availability.
- Intrusion Attempts: Hackers often probe networks for potential entry points through techniques such as port scanning and reconnaissance. Windows Firewall thwarts these intrusion attempts by detecting and blocking suspicious activity, preventing unauthorized access to sensitive resources and services.
Integration with Advanced Security Solutions
While the Windows Firewall provides essential protection against a broad range of threats, it’s most effective when complemented by additional security measures. For instance, organizations may deploy intrusion detection and prevention systems (IDPS) alongside the firewall to detect and respond to sophisticated attacks in real-time. Similarly, endpoint security solutions can enhance threat visibility and containment capabilities, augmenting the defenses provided by the firewall.
Conclusion
In an era where cyber threats loom large, the Windows Firewall stands as a stalwart guardian of your computer’s integrity and security. By leveraging advanced filtering techniques, customizable rulesets, and application-level control, it fortifies your system against a multitude of internet-based attacks, from malware and exploits to DoS assaults and intrusion attempts. However, to ensure comprehensive protection, it’s essential to integrate the firewall with a holistic security strategy that encompasses both network and endpoint defenses. With the Windows Firewall at the helm, you can navigate the digital landscape with confidence, knowing that your system is shielded from harm’s way.
For more training resources, check out our online training courses.
Check out our extensive IT book series.